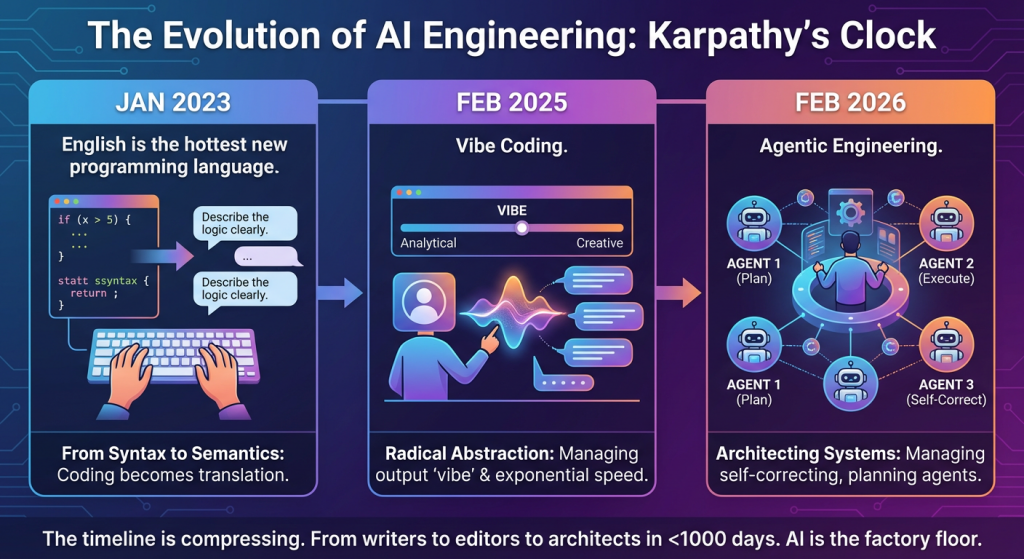
Andrej Karpathy’s nomenclature for the state of tech in AI has become the unofficial industry clock. Watching the terminology evolve over the last few years feels like watching innovation move from a crawl to a sprint:
Jan 2023: “English is the hottest new programming language.” The shift from syntax to semantics. We realized that the bottleneck wasn’t knowing where the semicolon goes, but being able to describe the logic clearly. Coding became a translation layer.
Feb 2025: “Vibe Coding.” The abstraction deepened. We stopped looking at the code entirely and started managing the ‘vibe’ of the output. It was the era of radical abstraction—prompting, iterating, and giving in to the exponential speed of LLMs.
Feb 2026: “Agentic Engineering.” The current frontier. We’ve moved from writing prompts to managing workers (agents). It’s no longer about a single interaction; it’s about architecting systems of agents that can self-correct, plan, and execute.
The timeline is compressing. AI isn’t just a pastime anymore; it’s the factory floor. We’ve gone from being writers to editors to architects in less than a thousand days!
We live in amazing times :-).
Google Gemini’s interpretation of the blog post in an infographic.